Proliferation of personal computing has assembled the struggle between consumers, developers, publishers, intellectual property right holders, retailers, and device manufacturers. Most users are lackadaisical while others diligent towards privacy and having control over their purchased devices and content they consume.
Having privacy and control is also portioned out by developers who are open source advocates. Readable peer reviewed source code is a source of security and privacy for everyone. This is partly the reason why developers don't enjoy sifting through code that is vague, manually obfuscated, dispersed, aliased, auto generated, and excessively separated between multiple files and directories.
At the heart of privacy and control is a file system and execution rights allocating core, originally strained from computing lab technicians. The heart of modern open source operating system generically known as Linux. A system designed to provide it's operator complete control over underlying hardware. Provided the user operator is a knowledgeable system admin, respects other users of the system and other nodes when system is on a network.
Along with open source operating system there are two most popular commercial operating systems. One type of system is a derivative of Linux and the other was born from a DOS prompt. These two variants of commercial systems provide convenience and ease of use to most users. Systems with these two operating systems are designed for home and small business users. Due to mass appeal and marketing most individuals are familiar with these system's visual user interface. Most of us take for granted how easy it is to "plug and play" peripherals to a personal computer with a commercial operating system. A purchase of an add on device from a retail store or a e-commerce site. A mouse, stylus, printer, scanner, or a external storage device.
A small business only disparages their own operation by using a home user license. Although the business may have initially adapted to use a commercial operating system with a familiar user interface.
Prior to downloadable software and App stores. Not too long ago software for personal computers came in a box containing discs licensed by software publisher. Software wasn't a platform constantly running on a user's system keeping track of a user's activity and updating some remotely stored user profile. For most, software was considered a tool or something to enjoy for a moment in time.
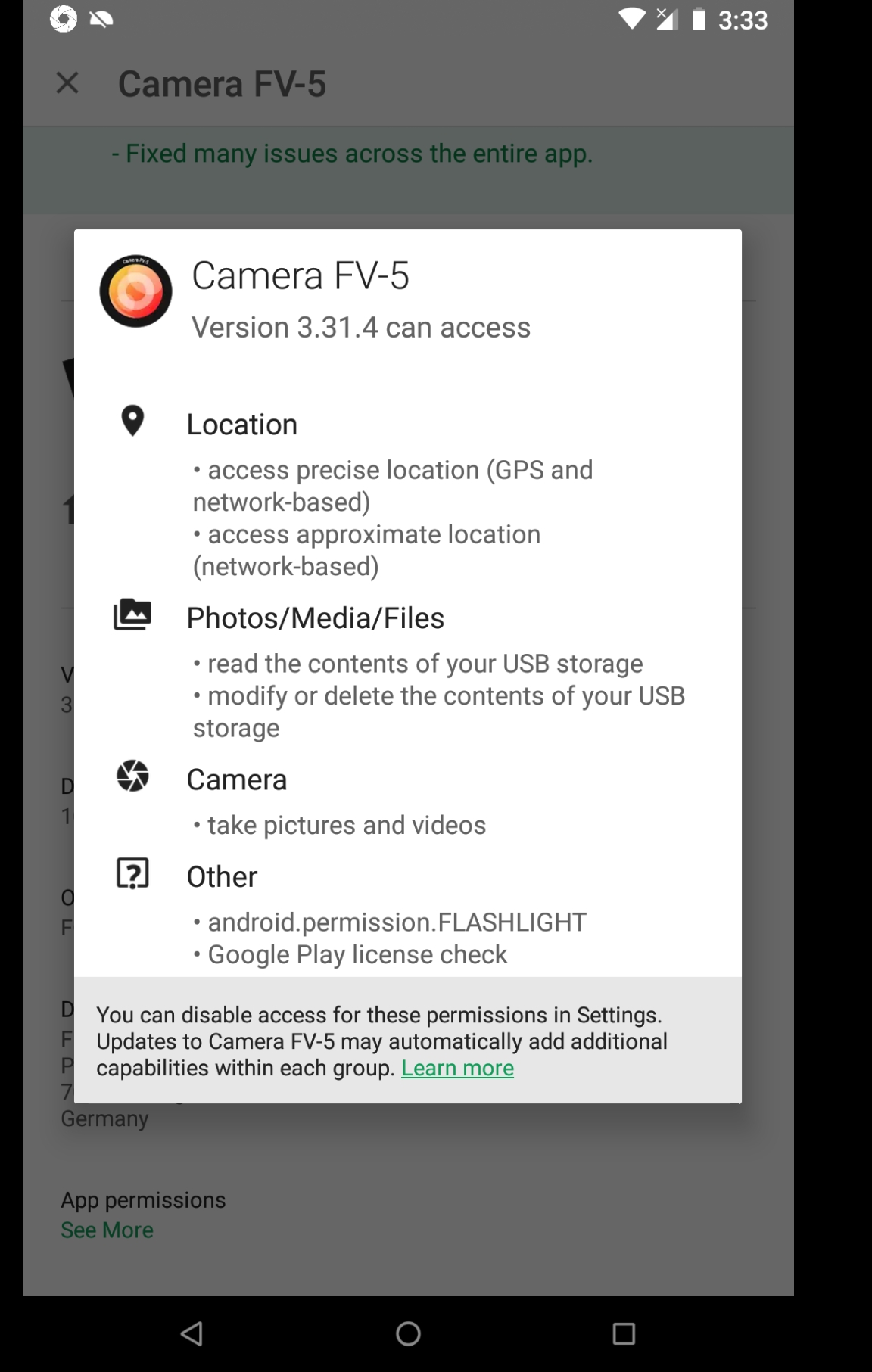
With the advent of smart personal mobile computing, rights and limits between a user, device manufacturer, operating system maintainers, store operators, and software publishers have become more elusive. Although Google Play store has done an amazing job of voluntarily publishing directly from application development configurations what device permissions are being used by an Application.
For example you are looking for a camera application with more features than the default App included with Android Operating System.

A free camera app
You scroll down and touch "Read More".
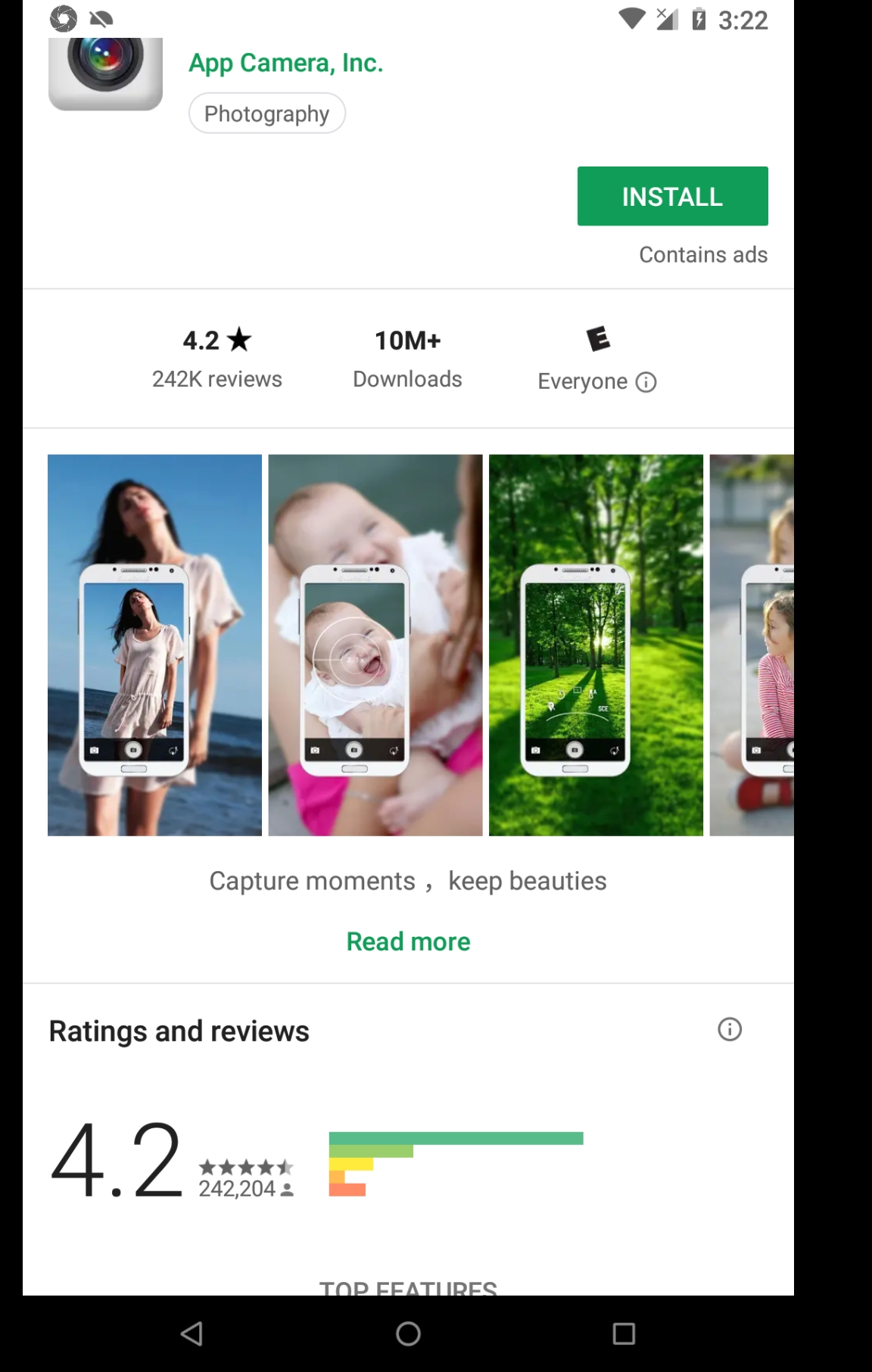
Read More
In the read more section of the App description you scroll down and touch on App permissions.
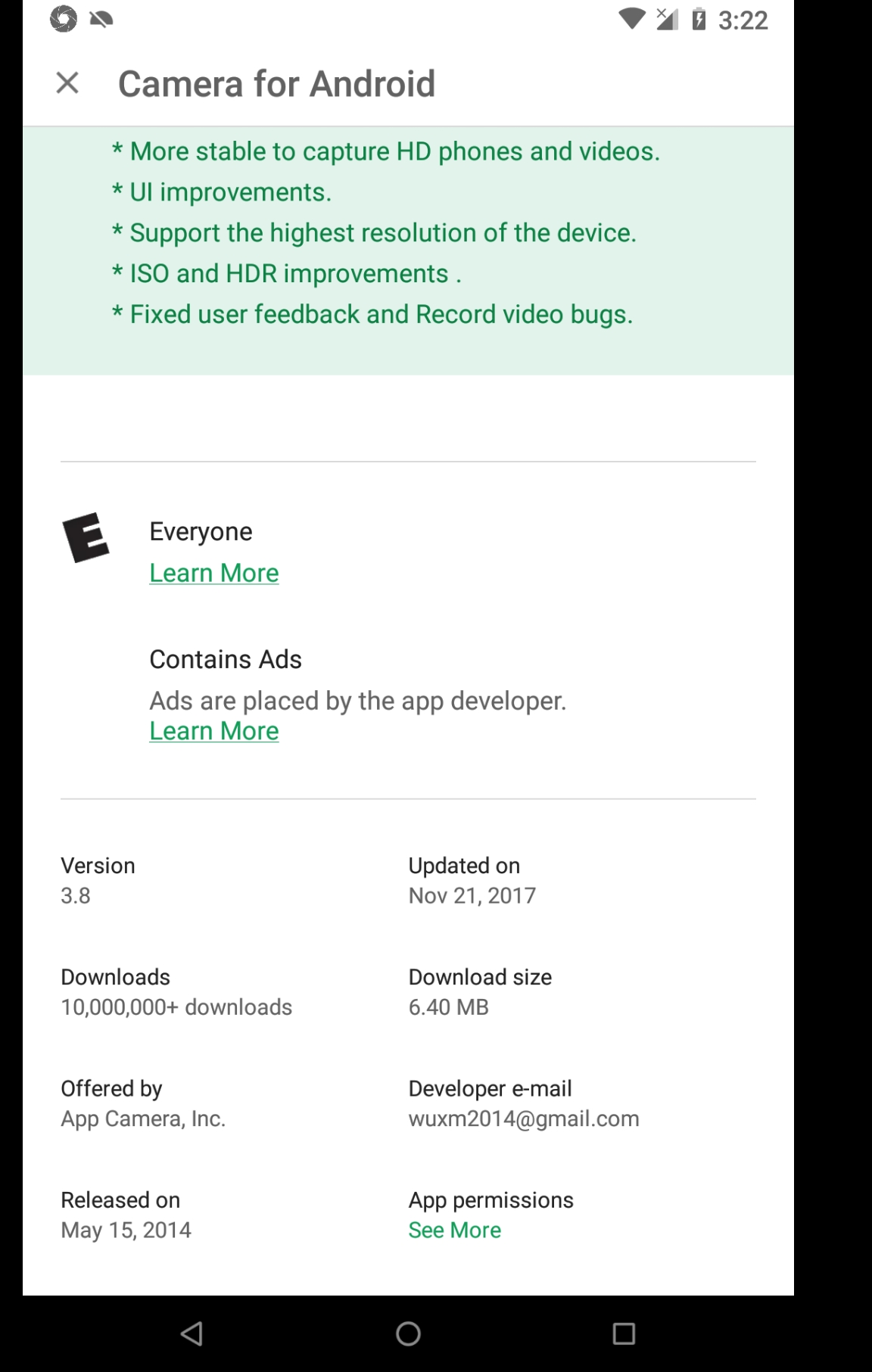
Scroll down to touch app permissions
Once App permissions is touched, a pop up dialog appears displaying device permissions that will be used by your selected Camera App.
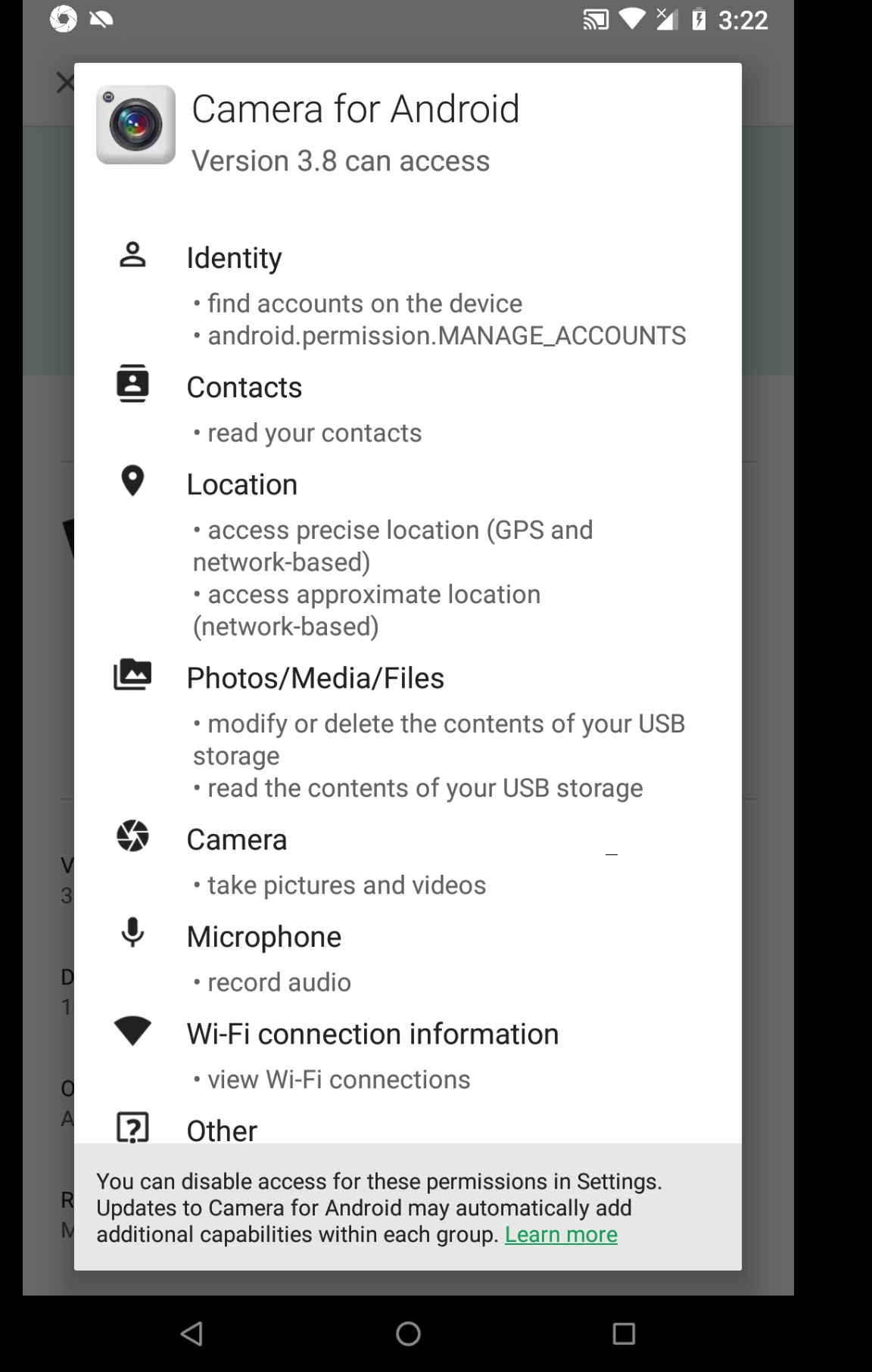
A free camera app
You decide to keep looking and see another Camera App.
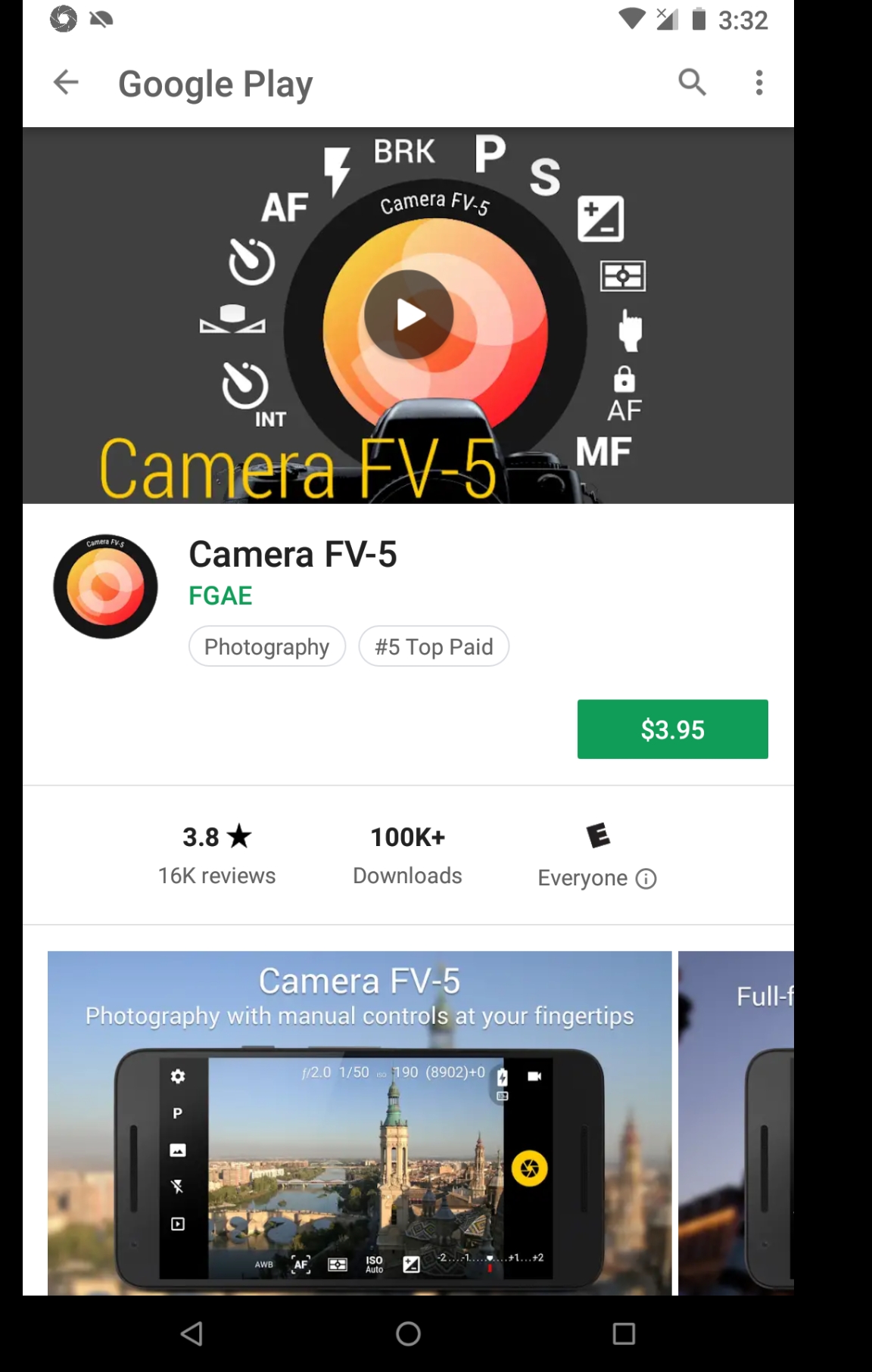
For pay camera app
You follow the same steps and get a pop up permissions dialog detailing device permissions required by the App.
For pay camera app
An Android device user can also set permissions for each application on their phone. With the latest visual interface enhancements made to Android operating system. You can simply swipe down from top edge of display to enable or disable, flash light, Wifi, Wireless data, Bluetooth and much more. Whither or not those permissions are honored by hardware manufacturer may be another issue.
A hardware designer and manufacturer known as Fairphone allows an Android device owner to physically remove components of a mobile device. Due to the modular hardware design you can simply use a basic screw driver to add remove hardware components.
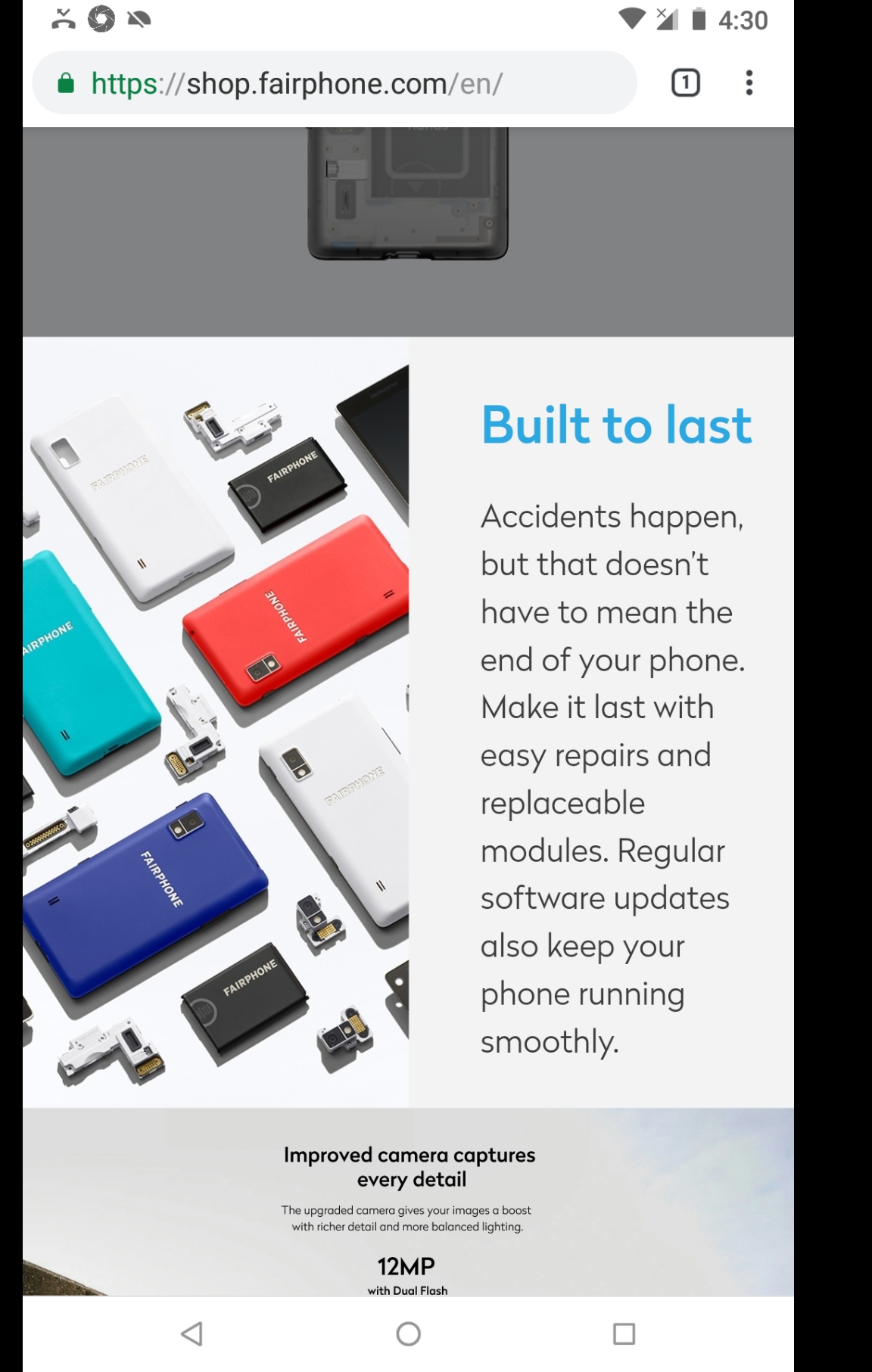
A modular phone
Besides hardware modularity there are future prospects of owning a GNU Linux based smart phone. Linux Operating System by foundation design, as many of you are aware, allows decoupling of applications from one another, and applications from core Operating System. Purism has released a Operating System PureOS for possible use with a smartphone device Librem 5
As envisioned and advocated by early adapters and pioneers of personal computing. Rights and limits are a serious matter. Computing will only be devalued without considering rights and limits of all parties involved. Otherwise most consumers would toss their devices in a recycling bin.
Images
-
- "Post picture of a dial lock" (http://www.merangue.com/Locks-50mm_Combination_Dial_Lock_1.html)
- "Screenshots" (play.google.com)
- "Screenshot" (shop.fairphone.com)
