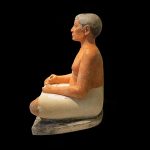
Ancient scribes must have had a tough life. What about us sitting in front of a desk for long periods of time?
For us in modern times. Sitting for..
HTML and CSS form the foundation of the web, as they are what the browser processes—HTML structures the content, CSS adds style, and PHP powers dyn..
Most social media apps are not self contained. This is mostly due to their nature. By their nature, to create trust between participants these apps r..
Chromebook is a valuble product at a low cost. In the past, before a user had access to a linux terminal required a hefty expense at a local computer..
Chromebook's linux development environment option creates a linux container. A sandbox for development.
Wouldn't it be neat and convenient to instal..